Blogs
Massive Supply Chain Attack - Axios 1.14.1 and 0.30.4
Over the night of March 30 to 31, 2026, a sophisticated cyberattack struck one of the most widely used software tools on the internet, a JavaScript library called Axios.
UTmessan 2026
SecureIT will be at booth B21 at UTmessan 2026 We at SecureIT are extremely excited to announce that we will have a booth at UTmessan on February 6th and 7th, 2026. This year, we will be located on the upper level in booth B21, right outside the Eldborg hall.
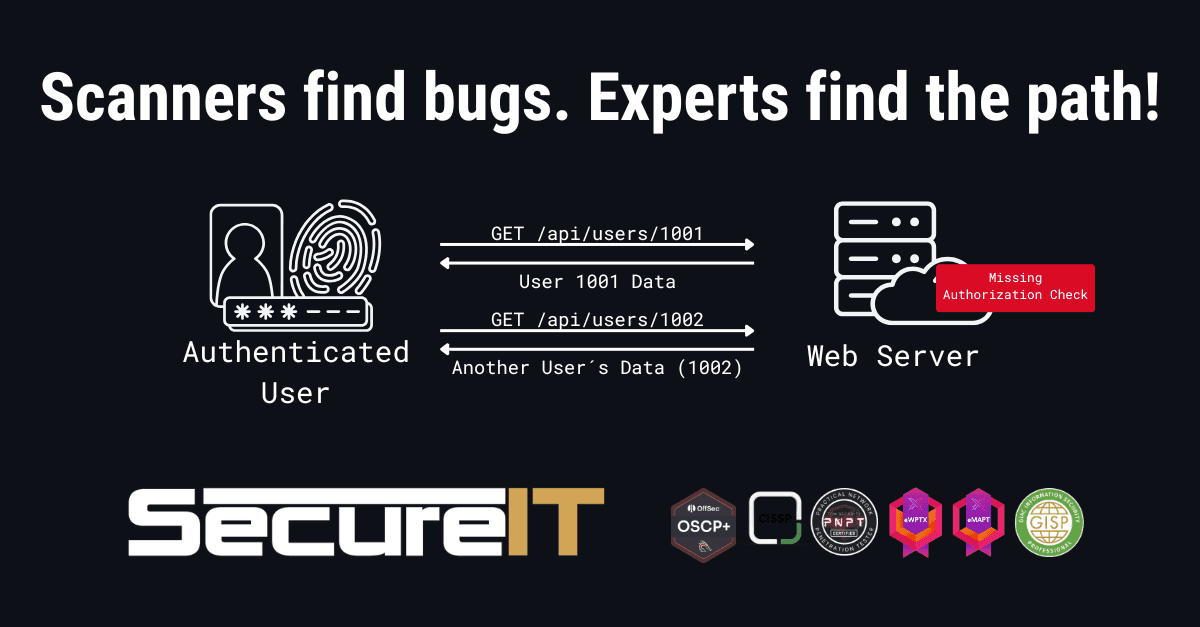
Beyond the Checklist: A Strategic Guide to Offensive Security
Most companies treat penetration testing as a "check-the-box" compliance task. But if you’re testing the wrong surface, you’re buying a false sense of security.

SecureIT - Top Vulnerabilities - December 2025
December 2025 had exploited issues across perimeter devices, email security appliances, Windows endpoints, browsers, developer platforms, and databases. Several flaws let attackers take over internet exposed systems or gain full control after a first foothold.
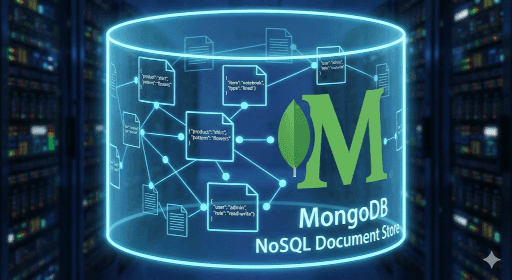
That Christmas 2025 MongoDB Vulnerability
What is MongoDB? • How bad is “MongoBleed” (CVE-2025-14847)? • Do I have MongoDB? • Is my MongoDB vulnerable?
Mobile Application Penetration Testing Explained
Most companies trust their mobile apps are secure but haven’t tested them. Here’s why that’s a costly mistake, and how a pentest reveals the truth.